Explanation of the authentication mechanisms for Ghostwriter’s JSON Web TokensDocumentation Index
Fetch the complete documentation index at: https://www.ghostwriter.wiki/llms.txt
Use this file to discover all available pages before exploring further.
Introduction
Authentication is handled via JSON Web Tokens (JWT). There are two methods for retrieving a JWT:- Submit credentials as described below and receive a JWT that is capable of interacting with Ghostwriter as the authenticated user
- Login via the web interface and generate a JWT with your preferred expiration date to use as an API token for automation
GRAPHQL_JWT_SECRET_KEY. If you plug a Ghostwriter JWT into a debugger like the one at https://jwt.io/, you will see something similar to the following:
User Tokens
User JWTs are generated with aLogin action. The resulting JWT holds the same privileges as the authenticated user. The user JWTs are valid for 15 minutes.
The
Login action is disabled for accounts with MFA configured. An account with MFA should use a generated API token (see below).API Tokens
You can also generate tokens by visiting their profile page and scrolling down to the “API Tokens” section. In this section, you can create new tokens, see all existing tokens, and revoke tokens you no longer need.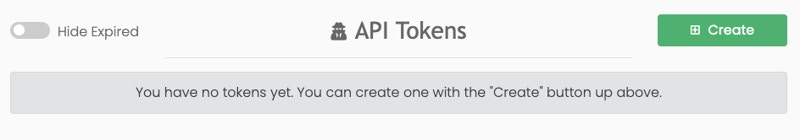
Login action is they have user-defined expiration dates. They are intended to be used for long-running automation tasks.
Token Authentication
Requests authenticate with theAuthorization header: Authorization: Bearer TOKEN
Hasura will connect to an authentication webhook before a request. The webhook takes several steps to thoroughly examine the JWT before allowing a request to proceed:
- Check the JWT is present
- Attempt to decode the JWT and verify the signature, audience, and expiration
- Verify the JWT contains the proper claims
- Finally, verify the user details are correct and that the account is still active
200 OK response with your requested data.
If the token is not accepted, the authorization webhook will return a 401 Unauthorized response with an error like this:
public role with the username anonymous. This is not a real user or role and is only used to manage access to resources designed to be accessed without authentication.
The only action available for this anonymous user is the Login action.